Thursday, August 31, 2017
The fight against synthetic identity fraud
Most people think of identity fraud as the theft of one person’s information. A widespread, fast growing threat is synthetic identity fraud. In synthetic identity fraud, a criminal might take the name of one person, the social security number of another and mix in some phony details to create a new fraudulent persona. The new personas, called “fullz” are then sold on the black market. Criminals use the fullz as they attempt account takeovers (ATOs) of legitimate existing accounts.
In a 2017 report by Javelin Strategy & Research, a record 15.4 million Americans were affected financial fraud in 2016, a 16% increase from 2015. Losses amounted to $16 billion dollars. Consumers pay for this loss in the form of higher prices and interest rates.
It's hard for consumers to spot this type of fraud in a credit report because some of the information resides in sub files, not visible in the parts of the report that consumers see. A consumer concerned about fraud will want to check their credit report several times a year. The social security numbers of children are prime targets, because the fraud may remain undetected for years.
One significant way financial institutions are fighting back against ATO fraud is with behavioral biometric authentication. With behavioral biometrics, a computer algorithm is used to learn the way you enter data, the speed of your typing, the pauses, the accuracy, even the pressure on a keyboard. If someone tries to open an account in your name, behavioral biometric authentication can identify the profile mismatch and shut the application down.
For consumers, good advice about protecting oneself against identity theft can be found on USA.gov: Identity Theft. How to protect yourself against identity theft and respond if it happens. An identity theft recovery plan is also downloadable.
How biometrics can fight synthetic identity fraud
By Kayla Matthews, August 28, 2017, on BiometricUpdate.com
Identity Fraud Hits Record Number of Americans in 2016
By Herb Weisbaum, Feb 2 2017, on NBCnews.com
Friday, August 25, 2017
Biometric payments a boon to school systems
Biometric payment systems are finding their way into the school system. A child can walk into the school cafeteria, choose a lunch meal, and touch a finger to a scanner to pay for their meal. No need for a small child to remember a PIN number. No worries about lost or stolen student cards.
Schools that have started using a biometric payment system have found their food service staff easily adapting to the new system. Lunch lines are more efficient and move faster. Food service reports are easier to prepare and submit to the federal government. Parents are able to keep track of their child’s spending habits at school.
The program is voluntary; parents can opt out. Also, privacy is maintained. The biometric data is encrypted and stored on an outside server, not by the school system.
Among the school districts in the US who are using, or have announced they’ll be adopting biometric payment systems are Newark, Pennsylvania, West Virginia’s Wood County and San Diego. Small schools as well as large benefit from using a biometric payment system. Biometric payment use in schools is growing internationally as well. Singapore is the latest country to announce the use biometric payments in schools, starting next year.
Singapore Schools to Connect Student Accounts to Fingerprints
Published August 22, 2017, FindBiometrics.com
IdentiMetrics to Provide Biometric Cafeteria Tech to Pennsylvania School District
Published July 17, 2017, FindBiometrics.com
San Diego School District Brings Biometrics to the Cafeteria
Published May 5, 2017, FindBiometrics.com
Friday, August 18, 2017
New breakthrough improves key step in forensic fingerprint analysis
Fingerprint analysis is partly subjective, and this can lead to errors. A 2009 study by the National Academy of Sciences (link below) found that analyzed results were not always repeatable. An experienced fingerprint examiner might disagree with their own past conclusions when examining the same set of prints at a later date. This kind of uncertainty can lead to innocent people being wrongly accused, and guilty people allowed to remain free.
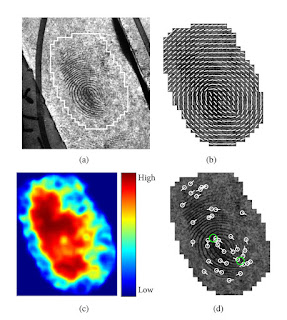
Scientists from NIST (National Institute of Standards and Technology) and Michigan State University have recently developed a new fingerprint analysis algorithm to automate a key step in fingerprint analysis, and greatly reduce errors that may be due to human subjectivity.
At a crime scene, found fingerprints, called latent prints, are often partial, distorted or smudged. The print may be left on something with a background pattern that makes it hard to separate the print from the background. When crime scene prints go for analysis, the first step is to judge how much useful information they contain. Prints deemed useful are submitted to the AFIS (Automated Fingerprint Identification System) database to search for matches.
If a fingerprint doesn’t have sufficient information, it could lead to erroneous matches. This is why the first step of evaluating latent prints is so important, and why the work has been done to create an algorithm to judge prints more consistently, accurately and efficiently. Time saved can be used to reduce the backlog of prints, solve crimes more quickly, and allow more time to be spent on challenging prints.
Scientists used machine learning to build their algorithm – training the computer to recognize patterns with known prints. Prints were given a quality score, from 1 to 5. In practice, prints with too low a quality score to create an accurate match should be pulled and not sent on to AFIS for matching.
What has enabled the breakthrough, besides advances in machine learning and computer vision, is the availability of a large set of fingerprint data for testing and analysis. The Michigan State Police allowed researchers the use of a large database of prints after the prints were stripped of identifying information to protect privacy.
Still, a larger data sample is desired to continue to refine the algorithm. Elham Tabassi, a NIST computer engineer states, “We’ve run our algorithm against a database of 250,000 prints, but we need to run it against million. An algorithm like this has to be extremely reliable, because lives and liberty are at stake.”
Scientists Automate Key Step in Forensic Fingerprint Analysis
Published August 14, 2017 on www.nist.gov
Strengthening Forensic Science in the United States: A Path Forward (2009)
National Research Council of the National Academies
Friday, August 11, 2017
Fingerprint-based background screening: a valuable tool for protecting children
Dean “Dino” Curcio, a Deer Park, IL resident, claimed to be a youth hockey coach so well known he wore a cap and sunglasses indoors at the local hockey arena to avoid being recognized. It’s a good thing he was not able to find a position with the coaching staff. On August 3rd he was arrested when it came to light he was wanted in Boulder, CO, on charges of sexual assault of a child by a person in a position of trust.
Examples like the above underscore how important it is that applicants for positions at youth serving organizations are carefully screened before hiring. A highly recommended screening first step is state and nationwide criminal history background checks. Two types of criminal history background checks are name-based and fingerprint-based.
Name based checks (based on name and SSN) are quick and accessible but have several limitations. An applicant may give a false name; have different last names, e.g. married name(s); have a common name; or there may be a type error in the database. Fingerprint-based checks reveal more information, and can catch individuals using an alias or legally changed name.
Criminal history background checks should be done in the state(s) the applicant has resided in, but a nationwide search is better. All organizations that serve children can have access to an FBI fingerprint-based background check. This is done through the state, allowed by the National Child Protection Act. Criminal history backgrounds checks alone won’t eliminate the risk of harm to children. But they are a critical tool in helping to minimize the risk to children.
The following statistics are from a report published by COPS (Community Oriented Policing Services). The report pdf download link follows.
- 58% of children are victimized by an acquaintance
- According to a LexisNexis® audit of over 3.7 million screenings from 2002-2007, more than 189,000 people with at least one criminal conviction attempted to gain employment or volunteer with a nonprofit organization. A registered sex offender attempted to obtain a position at a non-profit organization every 11.5 hours during the audit period.
- Of a subset of Child Pilot Safety applicants with criminal records:
○ 42% had a record in a different state
○ 23% applied with a different name
○ 6% applied with a different date of birth
○ 53.4% indicated that they did not have a criminal record, but one was uncovered
What You Need to Know About Background Screening
Authors: Kristen D. Anderson, Dawn Daly; Publication Date: 06/01/2013; Product ID: COPS-P260
Fugitive from sexual assault charges identified by Lake County residents after watching TV show
John Keilman, Lee V. Gaines and Frank S. Abderholden; August 4, 2017, Contact Reporters, Chicago Tribune
Friday, August 4, 2017
NamUS: aiding the search for the missing and the ID of the deceased unknown
NamUS (the National Missing and Unidentified Persons System) is a national, centralized repository to aid in the search for missing persons, the identification of the deceased unknown, and the retention of information on unclaimed deceased, for whom no next of kin has been identified or located. Among the biometric information that may be available are DNA, dental records and fingerprints. The public can access NamUS records, but the highest level of access is for law enforcement, medical examiners and coroners.
NamUS 2.0. The NamUS system is currently being upgraded to provide more information and better response in the event of a “critical incident,” such as catastrophic weather, a bombing, or an outbreak of disease. Among the upgrades planned to work towards this goal are:
• A central, secure data center for victim status (missing, injured or deceased)
• Real-time data and situational awareness to help emergency officials and guide their response
• The ability for state emergency managers to collaborate seamlessly with other states and federal resources
• A way for individuals to self-report as safe after a critical incident
• Free and secure access for local, state and federal officials
Visit the NamUS website for more information, including a fact sheet and an FAQ sheet.
Subscribe to:
Posts (Atom)